We are into the fourth quarter of 2018 and there are no signs of cyberattacks slowing down. Reports indicate that over the first three quarters of the year, cyberattacks were…
Read MoreLeaks
Two-factor authentication has been a near silver-bullet that prevents phishing attacks and online account thefts. It is very effective, as it provides the user a virtual “second password”, which disables…
Read More
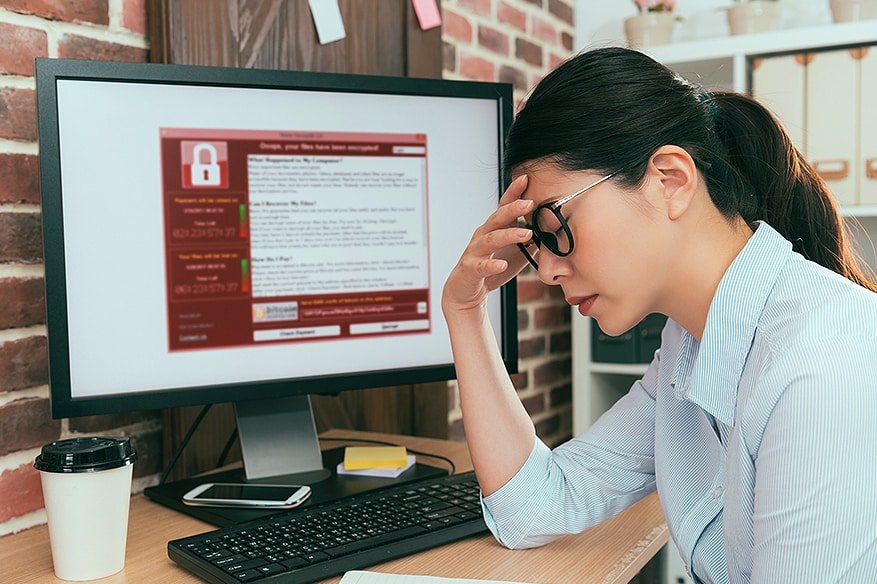
A new breed of cyberattacks- ransomware, fileless attacks and cold boot- have been impacting enterprise networks worldwide and proving to be a real headache to many. The ransomware menace The…
Read More
Deep web and privacy enthusiasts have a lot to rejoice for as the Tor Project has announced that their popular Tor Browser is now available for Android. Members of the…
Read More
U.S lawmakers, a bipartisan group of them, have joined hands in slamming Google’s CEO for declining to testify at the Senate hearing next week. Fox News reports- “On the same…
Read More
In a recent statement Google said that it has disabled 39 YouTube Channels associated with Iranian state broadcaster, which is running a political campaign to influence its viewers. Google said…
Read More
Thailand’s two big banks are the newest victims of a data leak involving 123,000 customer records. This happened on the backdrop of Thailand’s push for more and more cashless transactions….
Read More
Reddit is the most known discussion forum on the internet, and later today they announced that the hacker managed to fiddle with their system and have managed to leak user’s…
Read More
The United States, through its intelligence agencies, has uncovered a major cyber espionage vulnerability against software-based supply chain software. A supply chain attack refers to a cyber attack of unauthorized…
Read More
After a digital manual for an MQ-9A Reaper drone belonging to the U.S. military was recently copied online without authorization, it came up for sale on the darknet at just…
Read More