There are 3,4 million digital payment system users worldwide. This figure is almost equal to the number of social media users globally and the half of word’s population to date….
Read MoreData security

Picking up the best match for our needs was never as tough as it is these days. The market is flooded with so many options. To make things worse, each…
Read More

Whenever you come across a problem, Google it! Yes, this is what the 310 million people believe in when they want to get solutions for any difficulty they come across….
Read More
Don’t be lulled into the false sense of security by thinking your personal information is indeed private – you will be shocked to see how much about you is known…
Read More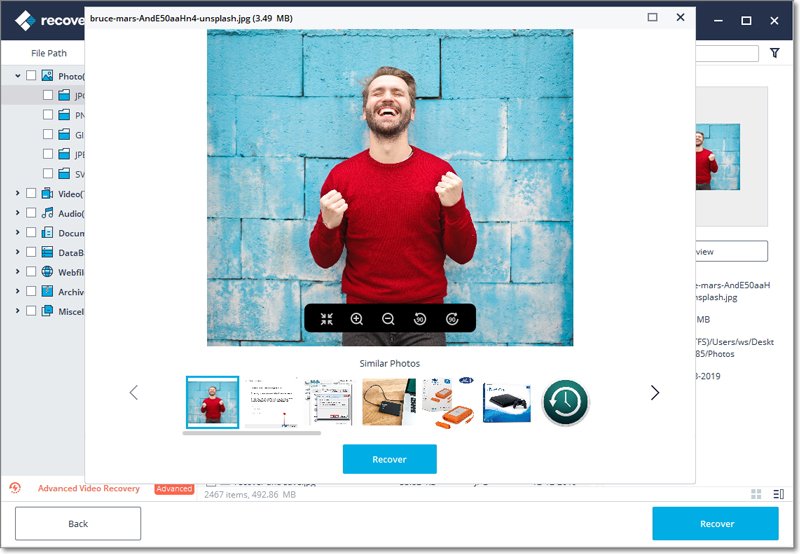
Most of the people store all their files in physical storage devices like pen-drives, hard-disks, memory cards, etc. Due to this, recovering files if having lost them or accidentally deleted…
Read More
Nowadays, cyberattacks are very common — you can read an attack or breach story every day. Though the cybercriminals may attack one of the organization’s devices, their end goal is…
Read More
Do you know how many iPhone users are there around the globe? It’s nearly 728 million! Yes, this is true, and there is no doubt that it has many fans…
Read More
Last week, NIST announced version 1.0 of its Privacy Framework, a tool designed to support organizations in managing their privacy risks. In September 2019, NIST released a revised draft Privacy…
Read More
The brute-force account cracking tool of Sentry MBA has been used to compromise user accounts. For nine months, an individual who was interested in a hack into the British National…
Read More
Apparently, without even decrypting it, DNS-over-HTTPS (DoH) traffic can be detected, a security researcher has discovered. The aim of the DoH protocol is to improve the overall Internet security by…
Read More