Future Investment Initiative Conference Website, Defaced, Now Restored

Saudi Arabia’s critical Future Investment Initiative conference website was hacked more than a week ago, Oct 22, 2018. Dubbed the “Davos in the Desert”, Future Investment Initiative is the middle eastern counterpart of the World Economic conference held in Davos. Which discusses the newest trends and middle-eastern countries actions towards changing market conditions for investments, politics and world events that can shape the future of the middle east.
Riyadh was chosen as the host city for the conference scheduled from Oct 23-25, 2018. Contrary to popular belief, Saudi Arabia and many Arab nations are heavily invested with the U.S. and the rest of the western world Tech firms, and their interest always has a huge say when it comes to decisions done by tech companies. The hacked FII site featured a modified image of the Crown Prince of Saudi Arabia beheading Jamal Khashoggi, a controversial Arab journalist. The latter apparently died due to the influence of Saudi officials in Istanbul.
The defaced image of the Crown Prince has a horrible caption stating: “Saudi regime is one of the sources for #Terrorism_Financing in the world. For the sake of security for children worldwide, we urge all countries to put sanctions on the Saudi regime. The regime, aligned with the United States, must be kept responsible for its barbaric and inhuman action, such as killing its own citizen Jamal Khashoggi and thousands of innocent people in Yemen. The medieval Saudi regime is one of the sources of #Terrorism_Financing in the world.”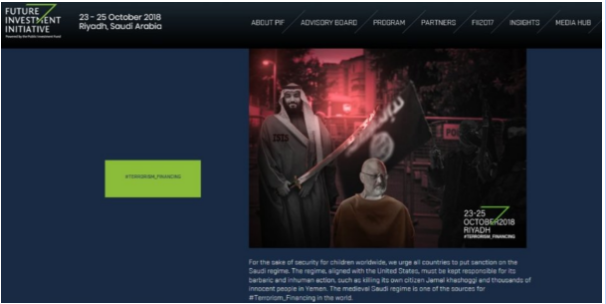
Hackers have demonized the Saudi regime, accusing the authorities of building terrorist cells, which allegedly caused 89,000+ Syrian deaths and 42,000+ dead Yemen nationals. As part of the defacement, the homepage of the said site was deliberately vandalized with information that highlights Saudi Arabia’s alleged crimes against humanity through the decades.
The Future Investment Initiate’s administrators were able to restore the original functionality of the site using a reliable backup. Any cyber attacks originating with terrorists or cyber jihadists in the near future are likely to be conducted either to raise money (e.g., via credit card theft) or to cause damage comparable to that which takes place daily from web defacements, viruses and worms, and denial-of-service attacks. While the impact of those attacks can be serious, they are generally not regarded as acts of terrorism. Terrorists have not yet demonstrated that they have the knowledge and skills to conduct highly damaging attacks against critical infrastructures (e.g., causing power outages), although there are a few indicators showing at least some interest.
Looking further into the future, it is difficult to know where cyber terrorism might lead. It is conceivable that cyber weapons will never draw the appeal of bombs and other physical weapons. Moreover, even if our critical infrastructures are not under imminent threat by terrorists seeking political and social objectives, they must be protected from harmful attacks conducted for other reasons such as money, revenge, youthful curiosity, and war. The owners of these infrastructures and their governments must defend against cyber attacks regardless of who may perpetuate them.